This is a spartan article about configuring Jitsi to run under Centos 7 (Centos 7.7.). on https://www.vultr.com/
The question was posted on Centos Forums and today it seems I have plenty of time (and the kids are asleep).
Let’s take this manual and try to modify it for Centos 7.7
https://github.com/jitsi/jitsi-meet/blob/master/doc/manual-install.md
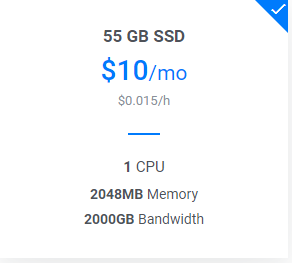
Our setup is as follows:
A Server in https://www.vultr.com with the following config
I have disabled the firewalls in Centos because I will be using the firewall option from my VMs in Vultr.
systemctl disable firewalld
systemctl stop firewalldDisabling IPv6 in my Centos box
I will not be using Ipv6 so for ease of configuration, I will disable it system-wide:nano /etc/sysctl.conf
# At the end of the file, add the following two lines
net.ipv6.conf.all.disable_ipv6 = 1
net.ipv6.conf.default.disable_ipv6 = 1
#Save and exit
sysctl -p
Several Settings
timedatectl set-timezone America/Panama
ln -s /usr/share/zoneinfo/America/Panama /etc/localtime
DNS entries
Jitsi expects some DNS entries, in my case
jitsi.nubeinterna.com
auth.jitsi.nubeinterna.com
focus.jitsi.nubeinterna.com
All of them point to the same public IP
Installing CertBot
yum install certbot -y
Generate SSL certificates for Prosody (we will use them later). I already had a Let’s Encrypt SSL Cert for one of the -d domains, so I will only add the auth. If this is your first time, add both -d
[root@jitsi ~]# certbot certonly --standalone --http-01-address 202.182.107.1 -d auth.jitsi.nubeinterna.com -d jitsi.nubeinterna.com
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator standalone, Installer None
Starting new HTTPS connection (1): acme-v02.api.letsencrypt.org
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
You have an existing certificate that contains a portion of the domains you
requested (ref: /etc/letsencrypt/renewal/jitsi.nubeinterna.com.conf)
It contains these names: jitsi.nubeinterna.com
You requested these names for the new certificate: auth.jitsi.nubeinterna.com,
jitsi.nubeinterna.com.
Do you want to expand and replace this existing certificate with the new
certificate?
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(E)xpand/(C)ancel: E
Renewing an existing certificate
Performing the following challenges:
http-01 challenge for auth.jitsi.nubeinterna.com
Waiting for verification...
Cleaning up challenges
IMPORTANT NOTES:
- Congratulations! Your certificate and chain have been saved at:
/etc/letsencrypt/live/jitsi.nubeinterna.com/fullchain.pem
Your key file has been saved at:
/etc/letsencrypt/live/jitsi.nubeinterna.com/privkey.pem
Your cert will expire on 2020-08-02. To obtain a new or tweaked
version of this certificate in the future, simply run certbot
again. To non-interactively renew *all* of your certificates, run
"certbot renew"
- If you like Certbot, please consider supporting our work by:
Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate
Donating to EFF: https://eff.org/donate-le
[root@jitsi ~]#
Prosody
1- We need to enable EPEL repositoryrpm -Uvh https://download.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpm
2- Install Prosodyyum install prosody
Accept the lua dependencies that need (bitop, expat, filesystem, sec, socket)
After installation, config file will live in /etc/prosody/prosody.cfg.lua. But you usually do not need to touch it. Instead, let’s create a specific config for our jitsi server.
cd /etc/prosody/conf.d
touch jitsi.nubeinterna.com.cfg.lua
nano jitsi.nubeinterna.com.cfg.lua
-- this is a comment inside the cfg file
-- add your domain virtual host section
-- Remember to change YOURSECRET1 and YOURSECRET2
-- Also need to change the virtualhost
VirtualHost "jitsi.nubeinterna.com"
authentication = "anonymous"
ssl = {
key = "/etc/prosody/certs/privkey.pem";
certificate = "/etc/prosody/certs/fullchain.pem";
}
modules_enabled = {
"bosh";
"pubsub";
}
c2s_require_encryption = false
-- add domain with authentication for conference nubefocus user
VirtualHost "auth.jitsi.nubeinterna.com"
ssl = {
key = "/etc/prosody/certs/privkey.pem";
certificate = "/etc/prosody/certs/fullchain.pem";
}
authentication = "internal_plain"
-- add nubefocus user to server admins
admins = { "nubefocus@auth.jitsi.nubeinterna.com" }
-- Component Configuration
Component "conference.jitsi.nubeinterna.com" "muc"
Component "jitsi-videobridge.jitsi.nubeinterna.com"
component_secret = "YOURSECRET1"
Component "focus.jitsi.nubeinterna.com"
component_secret = "YOURSECRET2"
-- save text fileIf you are using Let’s Encrypt certificates like me, then copy the .pem files to the certs directory of prosody:
cp /etc/letsencrypt/live/jitsi.nubeinterna.com/fullchain.pem /etc/prosody/certs/fullchain.pem
cp /etc/letsencrypt/live/jitsi.nubeinterna.com/privkey.pem /etc/prosody/certs/privkey.pem
cd /etc/prosody/certs/
chown root:prosody fullchain.pem
chown root:prosody privkey.pem
chmod g+r privkey.pem
3- Generate SSL certificates for the domain, type at the prompt. This step can be seen as redundant since we generated Let’s Encrypt certificates, but I want the Prosody tool to automatically create the entries in the configuration files.prosodyctl cert generate jitsi.nubeinterna.com
prosodyctl cert generate auth.jitsi.nubeinterna.com
Configuration file will be written to /var/lib/prosody/
and Certificate will be written to /var/lib/prosody/
4- Skip this step if using Let´s Encrypt.
Add auth.jitsi.nubeinterna.com to the trusted certificates on the local machineln -sf /var/lib/prosody/auth.jitsi.nubeinterna.com.crt /etc/pki/ca-trust/source/auth.jitsi.nubeinterna.com.crt
Update the local certificates list (using Centos update-ca-trust, update-ca-certificates is Debian’s way)update-ca-trust extract
(no ouptput will be provided if it’s OK)
5- Create conference nubefocus user (you can call it something else)prosodyctl register nubefocus auth.jitsi.nubeinterna.com YOURSECRET3
6- Restart prosody XMPP server with the new config. This will make it run at TCP 5347. This port will receive connections from JITSI VideoBridge and JITSI Conference Focus.prosodyctl restart orsystemctl restart prosody
Also,
systemctl enable prosody
Configure and Install NGINX
yum install nginx -y
Note: A LOT of packages will be downloaded!!!
Configure nginx
cd /etc/nginx/conf.d/
touch jitsi.nubeinterna.com.conf
nano jitsi.nubeinterna.com.conf
# Insert this into the file
server_names_hash_bucket_size 64;
server {
listen 0.0.0.0:443 ssl http2;
#listen [::]:443 ssl http2;
server_name jitsi.nubeinterna.com;
ssl_certificate /etc/letsencrypt/live/jitsi.nubeinterna.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/jitsi.nubeinterna.com/privkey.pem;
# set the root
root /opt/jitsi-meet;
index index.html;
location ~ ^/([a-zA-Z0-9=\?]+)$ {
rewrite ^/(.*)$ / break;
}
location / {
ssi on;
}
# BOSH, Bidirectional-streams Over Synchronous HTTP
# https://en.wikipedia.org/wiki/BOSH_(protocol)
location /http-bind {
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_pass http://localhost:5280/http-bind;
proxy_set_header Host $http_host;
}
# external_api.js must be accessible from the root of the
# installation for the electron version of Jitsi Meet to work
# https://github.com/jitsi/jitsi-meet-electron
location /external_api.js {
alias /opt/jitsi-meet/libs/external_api.min.js;
}
}
# save the text file and do a systemctl restart nginx
systemctl enable nginxResults so far
You should have Prosody and NGINX running, but not really useful. Now, let the real fun begin.
Installing Jitsi VideoBridge
The Jitsi VideoBridge is a JAVA application, so we need to perform several steps to make it work. (un)fortunately the guys from JITSI still use Java8 in all their documents. I read some posts that «it works» with JRE11 and several issues with JRE13. So I will use JRE8, test it and only if I have a working config I will try to update JRE to 11 then to 13.
Visit https://download.jitsi.org/jitsi-videobridge/linux to determine the current build number, download to the /opt/ directory and unzip it:
wget https://download.jitsi.org/jitsi-videobridge/linux/jitsi-videobridge-linux-{arch-buildnum}.zip
unzip jitsi-videobridge-linux-{arch-buildnum}.zip
Let’s move the unzipped directory to /opt/mv jitsi-videobridge-linux-{arch-buildnum} /opt/
Java 8 is still the most widely-used version of Java. The JITSI manual states that it wants to install Java 8, install it by running the following command:yum install java-1.8.0-openjdk
NOTE: When installing keep in mind that you need JRE >= 1.7.
According to the instructions we need to create a special file
mkdir -p ~/.sip-communicator cat > ~/.sip-communicator/sip-communicator.properties << EOF org.jitsi.impl.neomedia.transform.srtp.SRTPCryptoContext.checkReplay=false # The videobridge uses 443 by default with 4443 as a fallback, but since we're already # running nginx on 443 in this example doc, we specify 4443 manually to avoid a race condition org.jitsi.videobridge.TCP_HARVESTER_PORT=4443 EOF
Now we start the JAVA videobridge application
Choose your procedure to start the java app. ./jvb.sh --host=localhost --apis=xmpp,rest --domain=jitsi.nubeinterna.com --port=5347 --secret=YOURSECRET1 & or ./jvb.sh --host=localhost --apis=xmpp,rest --domain=jitsi.nubeinterna.com --port=5347 --secret=YOURSECRET1 > /var/log/jvb.log 2>&1 &
Install Jitsi Conference Focus (jicofo)
We need Apache Maven for this:yum install maven
cd /opt
yum install git
git clone https://github.com/jitsi/jicofo.git
cd /opt/jicofo/
Now we need to build the package with MAVENmvn package -DskipTests -Dassembly.skipAssembly=false
Go grab a coffee.
You should end up with something like this:
[INFO] Building zip: /opt/jicofo/target/jicofo-1.1-SNAPSHOT-archive.zip
[INFO] Building jar: /opt/jicofo/target/jicofo-1.1-SNAPSHOT-jar-with-dependencies.jar
[INFO] ————————————————————————
[INFO] BUILD SUCCESS
[INFO] ————————————————————————
[INFO] Total time: 10:45.261s
[INFO] Finished at: Mon May 04 06:27:19 UTC 2020
[INFO] Final Memory: 92M/444M
[INFO] ————————————————————————
[root@jitsi jicofo]#
Now we unzip it and run it
unzip target/jicofo-1.1-SNAPSHOT-archive.zip
cd jicofo-1.1-SNAPSHOT'
./jicofo.sh --host=localhost --domain=jitsi.nubeinterna.com --secret=YOURSECRET2 --user_domain=auth.jitsi.nubeinterna.com --user_name=nubefocus --user_password=YOURSECRET3 > /var/log/jicofo.log 2>&1 &
So, the VideoBridge and the Jitsi Conference Focus should be up and running with no issues.
Now, onto Jitsi-Meet
Install development tools
yum install gcc-c++ make -yIn order to configure JITSI-Meet we need npm and NodeJS but do not install it using yum just yet. We need to perform a manual install from the nodesource repositoy.
Install NodeJS 14.x and NPM 6.Xcurl -sL https://rpm.nodesource.com/setup_14.x | bash -
yum install -y nodejs
cd /opt/
git clone https://github.com/jitsi/jitsi-meet.git
cd jitsi-meetnpm installnpm update
make
Now we need to modify this config file
nano /opt/jitsi-meet/config.js
Here is my configuration, modify according to yours.
/* eslint-disable no-unused-vars, no-var */
var config = {
// Connection
//
hosts: {
// XMPP domain.
domain: 'jitsi.nubeinterna.com',
// When using authentication, domain for guest users.
// anonymousdomain: 'guest.example.com',
// Domain for authenticated users. Defaults to <domain>.
// authdomain: 'jitsi-meet.example.com',
// Jirecon recording component domain.
// jirecon: 'jirecon.jitsi-meet.example.com',
// Call control component (Jigasi).
// call_control: 'callcontrol.jitsi-meet.example.com',
// Focus component domain. Defaults to focus.<domain>.
focus: 'focus.jitsi.nubeinterna.com',
// XMPP MUC domain. FIXME: use XEP-0030 to discover it.
muc: 'conference.jitsi.nubeinterna.com'
},
// BOSH URL. FIXME: use XEP-0156 to discover it.
bosh: '//jitsi.nubeinterna.com/http-bind',
// Websocket URL
// websocket: 'wss://jitsi-meet.example.com/xmpp-websocket',
// The name of client node advertised in XEP-0115 'c' stanza
clientNode: 'http://jitsi.org/jitsimeet',
// The real JID of focus participant - can be overridden here
// focusUserJid: 'focus@auth.jitsi-meet.example.com',
// Testing / experimental features.
//
After this step, restart nginx because Jitsi-Meet is served by nginx.
systemctl restart nginx
Final Testing
using your computer web browser goto https://jitsi.nubeinterna.com and create a channel
Then use your Jitsi cellphone app and change the settings to reflect the server that you wish to connect to: https://jitsi.nubeinterna.com and connect to same channel.
Everything works except two things:
1- Blur background (BETA) is unreliable. no further testing has been done.
2- When Disabling peer-to-peer in jitsi cellphone app settings, it does not let me transmit video from my cellphone. perhaps it’s because both devices are in the same NATed LAN and Jitsi server is in Public Internet. In jitsi cellphone app, peer-to-peer is enabled by default.
To Do:
Upgrade JRE version from 8 to 11 and then to 13
Enhance this document. It is very spartan.
Fine tune Jitsi/JRE parameters. This is a small VM and may hit other issues under load.
And finally what I love form Vultr.com is that writing and testing this article only cost me USD 0.65 in VM runtime.
I will keep the VM running for a few more days so I can enhance the writing of this article.
BTW Suggestions for a better blog theme (free/nonfree) are always welcomed.
Hope it helps!!